Privateness is a proper, not a privilege. This text is for web3 builders, founders, and builders preferring to function anonymously for quite a lot of causes.
The primary part of this web3 privateness information will educate you shield your on-line exercise in an effort to stay nameless from third events and individuals who would quite observe you than mind their own business.
It’s harmful to be alone, take this recommendation!

Browser Splitting
Step one is to modify browsers to your crypto-anon id. You may, for instance, use Brave for private use and Mozilla Firefox for crypto actions.
Why Ought to You Use a Completely different Browser?
Due to monitoring expertise, it’s best to compartmentalize your browsers primarily based in your exercise. Monitoring expertise is primarily used for focused promoting and might jeopardize your anonymity.

Browser fingerprinting, for instance, can acquire extremely private details about the web sites you go to and your browser configuration, and it is significantly troublesome to keep away from. You may be taught extra by studying this study.
Primarily, a web site or a 3rd social gathering can immediately join your nameless exercise along with your doxxed exercise and retailer this info, which may then be stolen or doxxed in a knowledge breach (which occurs, like, on a regular basis).
Your digital fingerprint is normally offered to advertisers, which signifies that anybody should purchase your complete behavioral profile and on-line exercise, compile the information, and procure your IRL id.
Learn how to Defend Your self Towards Browser Fingerprinting
To start, solely use one browser to your nameless persona and by no means combine it with different on-line actions. Set it as your default browser to keep away from utilizing your doxxed account to log in to apps and chats.
Then:
- Flip off Javascript (most trackers run on it).
- In your browser’s settings, disable monitoring scripts.
- Incorporate privateness extensions, equivalent to Privacy Badger, NoScript and Ghostery.
- By default, use Tor or Courageous for elevated privateness.
- Use this tool from the Digital Frontier Basis to check your browser’s safety.
-
Inform web sites that need to observe you to go off and disable cookies in your browser.
(No, you don’t “worth my privateness” in case you obtained this banner in your web site, as a result of in case you actually did, you would not want this banner within the first place). -
Use a non-public browser and privateness pleasant search engines.
Further Ranges of Privateness
You’ve gotten three different choices for enhancing your safety setup:
- Create a brand new account that may solely be used to your different actions.
- In your current pc, set up a separate VM (Digital Machine).
- Use a totally totally different system to your nameless persona.
When networking anonymously, securely managing your social accounts is important to keep away from doxxing your self or revealing an excessive amount of about your self.
Involuntarily Doxxing
Involuntarily doxxing happens once you doxx your self and unconsciously reveal cross info that may result in your doxxed account.
Learn how to Keep away from It
First, create an nameless account with a brand new e mail deal with, and don’t log in with the identical browser. When you use Twitter, keep away from connecting any cellphone quantity, or do it by utilizing disposable ones (like Google Voice or an analogous service).
Take applicable motion relying on who you’re making an attempt to cover your id. Your loved ones? Your authorities? The remainder of the cryptocurrency neighborhood?
Twitter shows your followers primarily based on the date you started following them, so do not begin by following or partaking with your mates or with small accounts, since narrowing your id will likely be easy. All the time observe large accounts first, and wait some time earlier than partaking with individuals who can join you to your real-life id.
Time Zones
A stalker can use your time zone to pinpoint your actual location. It’s not good to your privateness or safety if somebody is aware of your time zone and begins including clues gleaned out of your on-line exercise.
Here is Why You Should not Doxx Your Time Zone
You by no means know who’s studying and interesting along with your content material. Folks turn out to be enraged on the web for causes you may by no means perceive or care about. Nevertheless, it’s particularly harmful once you’re concerned in a undertaking and start to draw opponents and detractors.
Additionally, in case you’re working in a rustic the place crypto is banned, it’s best to reduce the clues about your location to keep away from getting sanctioned. You by no means know who’s monitoring your exercise.
To guard your self and your loved ones, it’s best to keep away from giving them any details about your location.
Learn how to Cover Your Time Zone
These are the choices out there to you:
- In your pc, change the timezone (not likely handy, however works effectively).
- Keep away from posting screenshots of chats as a result of they reveal your timezone.
- Moderately than posting instantly, schedule some tweets for if you find yourself sleeping.
- On GitHub, change the
GIT_COMMIT_DATEand/or theGIT_AUTHOR_DATE. - Don’t focus on your environment (e.g. climate, political actions, and many others).
- Don’t particular characters in your keyboard which might be particular to your language.
Every part you put up on-line comprises details about your self. All the time preserve this in thoughts when performing duties, particularly when importing photographs.
What Does the Metadata Include?
Every part, from the digital camera used to take the picture to the precise location the place it was taken.
For instance, contemplate this picture (a glamorous selfie from the writer):
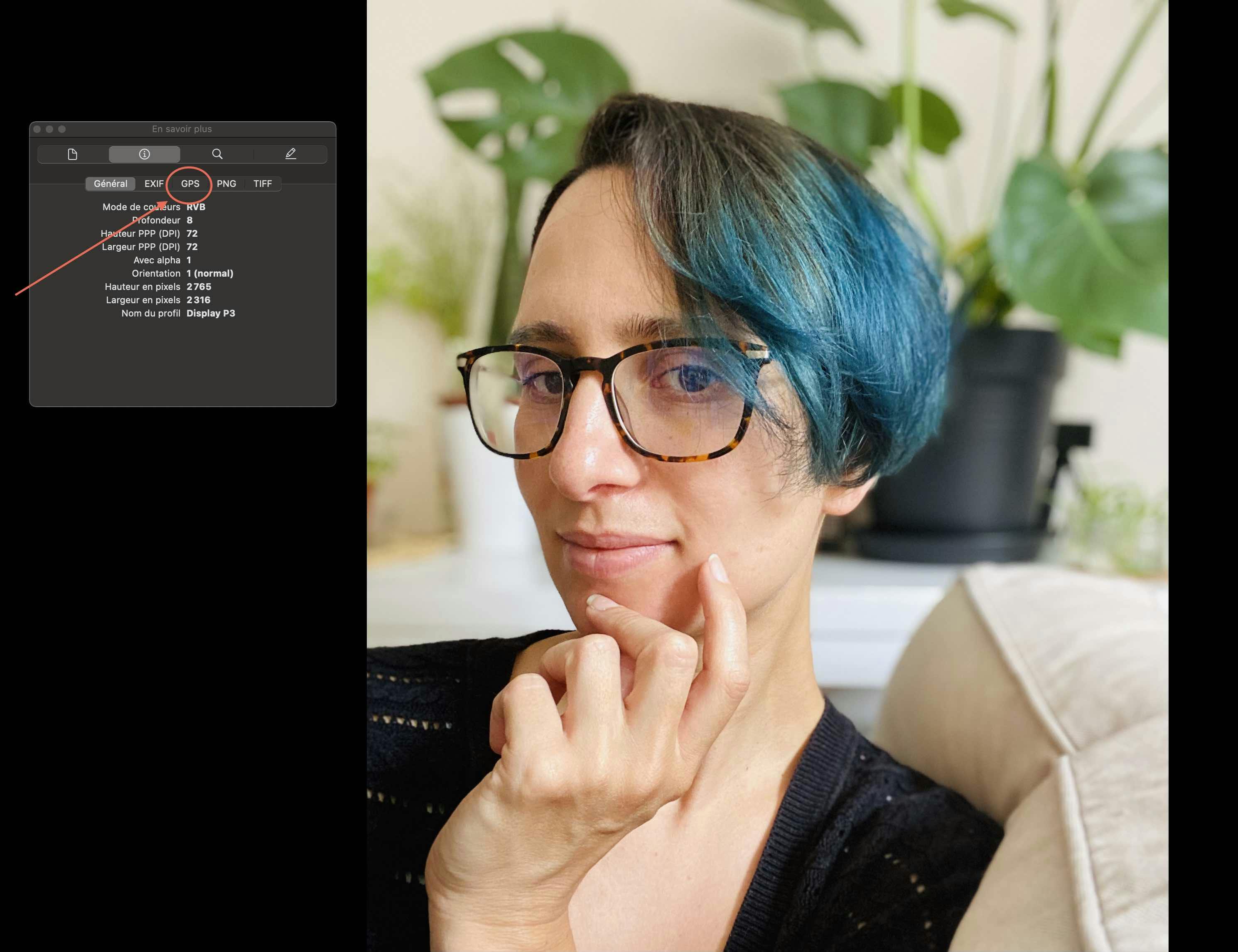
As you may see, I had my geolocation turned on once I took this image, due to this fact the GPS metadata is contained within the image, displaying the precise location the place it was taken, which is… my residence. Oops?
Learn how to Take away Metadata From a Image
Take away metadata from photographs earlier than posting, or add a screenshot as an alternative of the unique. On Mac, use the inspector (Preview > Instruments > Present Inspector > information field > GPS > « Take away location ») to take away GPS information from any picture.
Use Exif Remover or related web sites/apps to take away any remaining information. It ought to be famous that some web sites, equivalent to Twitter, take away the EXIF metadata from photographs, whereas others do not.
Hyperlink Monitoring
Few individuals are conscious that by clicking on a hyperlink, they might be revealing their location to a 3rd social gathering. Many web actions can reveal your IP deal with. Because of this, it’s best to use a VPN or Tor (extra on that later).
As a substitute of Clicking, Copy and Paste
For instance, you do not need to click on a hyperlink and find yourself logging into an app (like Discord) with the fallacious account. Copy and paste any hyperlink into the suitable browser. You’ll restrict monitoring, reveal your IP deal with, and blend social accounts this fashion.
VPN/Tor: What, How, and Why?
You would be stunned how usually you reveal your IP deal with on the Web by clicking on publication hyperlinks, filling out varieties, or downloading one thing.
Not solely that, however your web service supplier can monitor your on-line exercise (this is named ISP tracking). When you dwell in a rustic the place cryptocurrency is prohibited, you may must spoof your web exercise with Tor or a VPN.
Tor is a free anonymity service. It focuses on hiding who you might be on the Web. In the meantime, a VPN solely hides what you do and requires fee. Whereas TOR is slower, a VPN is quicker.
Select primarily based in your wants, and in case you use each, keep in mind to first connect with Tor earlier than activating the VPN.
Examine VPNs that respect your privateness by limiting the data they acquire about you. Thus far, Mullvad is the one one I would suggest.
Your Anon Pockets
You may want funds to get began on web3 along with your nameless persona. When you purchase tokens with a bank card, don’t ship them on to your anon pockets as a result of it’lll be simple to hyperlink your IRL id to it. Use Twister Money or Monero as an alternative.
Learn how to Use Twister Money
Tornado Cash is a decentralized protocol that gives transaction privateness for crypto transfers, and works with the next networks:
-
Ethereum Mainnet
-
Binance Good Chain
-
Polygon Community
-
Optimism
-
Arbitrium One
-
Gnosis Chain
-
Avalanche Mainnet
-
Ethereum Goerli
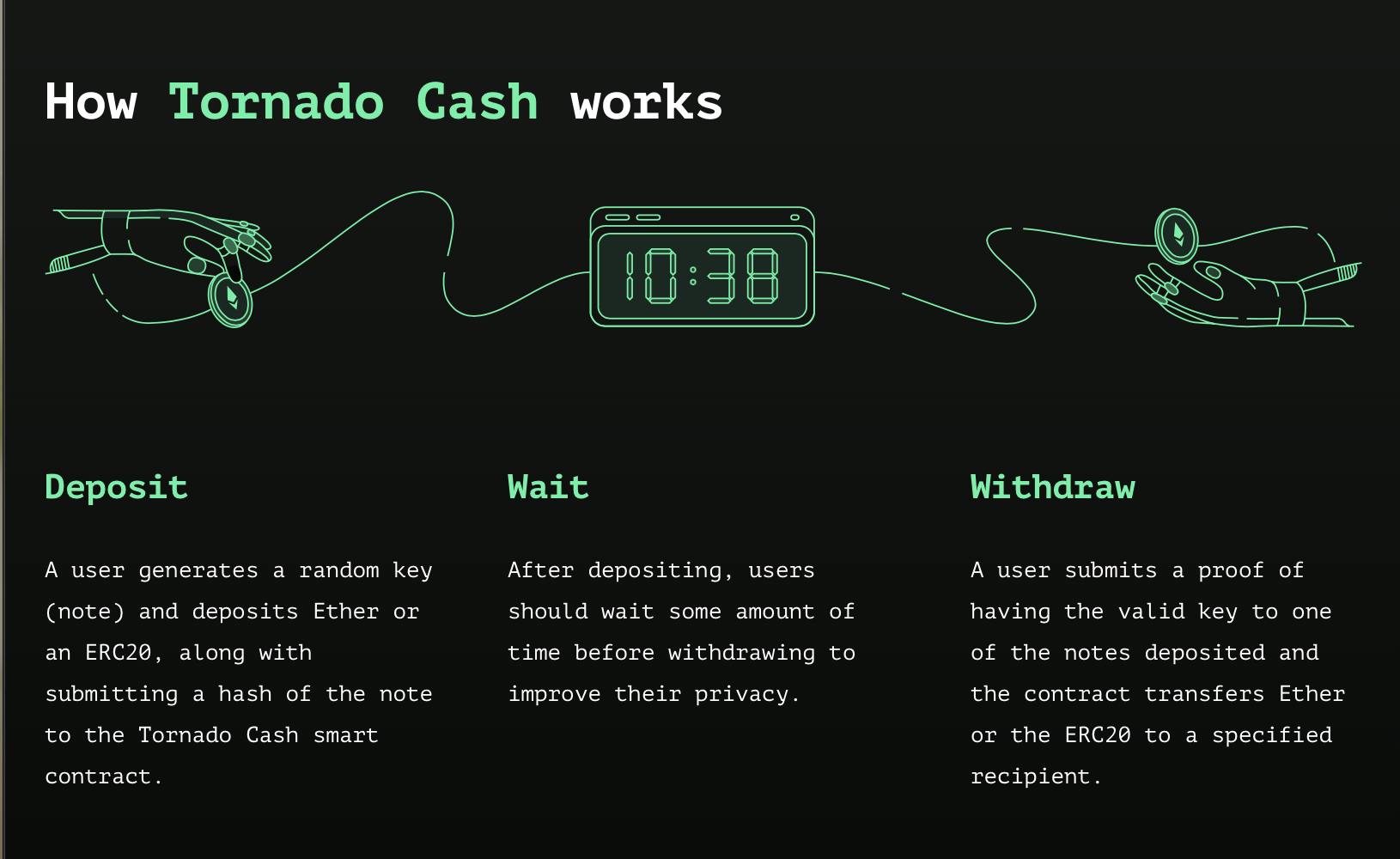
You’ll want to attend earlier than withdrawing your funds, in any other case, it’ll be simple to trace the precise quantity you deposited and retrieved to a different deal with. Wait between two weeks and a month earlier than withdrawing to your anon deal with.
Utilizing Monero for Personal Transfers
As a substitute of utilizing Twister Money, you need to use decentralized finance (DeFi) to transform your funds to Monero after which switch them to a different chain. Monero achieves anonymity by implementing privacy-enhancing applied sciences that obfuscate transactions. Which means that nobody can observe your Monero exercise, even on a public ledger.
Nevertheless, these strategies of reaching privateness are weak to threats and efforts to uncover hidden activities. This fixed strain additionally provokes communities of privacy-conscious builders to build and patch harder to counter those efforts.
Conclusion: This Is Solely the Starting
Sustaining anonymity is a crucial job, and it’s additionally mandatory relying in your state of affairs creating on web3.
Builders, founders, and different actors should be capable to shield their households and themselves from malicious actions directed at them. Keep protected on the market!

This text is part of the Hashnode Web3 blog, the place a staff of curated writers are bringing out new sources that will help you uncover the universe of web3. Test us out for extra on NFTs, DAOs, blockchains, and the decentralized future.









